Beyond Core Protocols: Agentic Commerce, Agent Experience, and What's Next
How ACP and AP2 enable secure transactions, why APIs need agent-optimized design, and the error handling patterns that keep multi-agent systems running in production...
Welcome to Part 2 of a comprehensive guide to understanding the protocol landscape for multi-agent systems
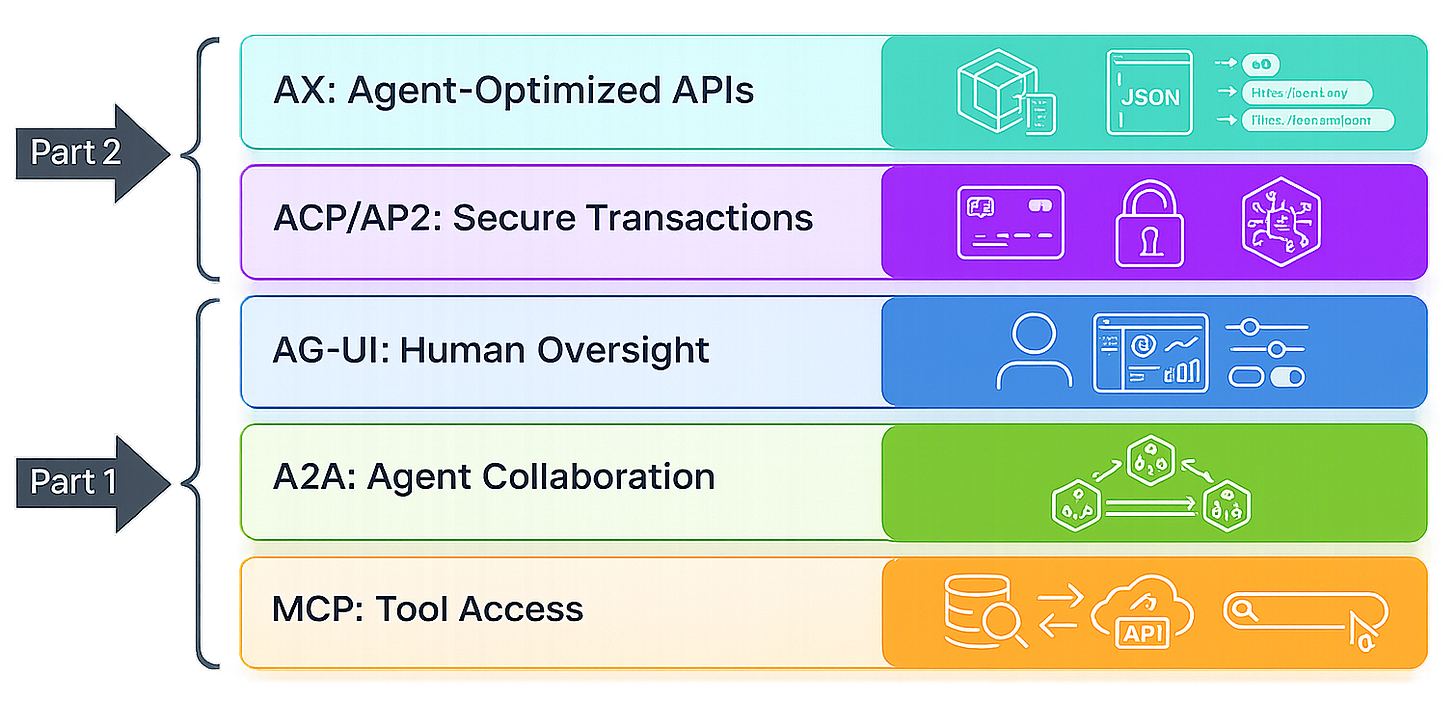
In Part 1, I covered the three core protocols that handle internal multi-agent coordination:
MCP standardizes how agents access external tools
A2A enables flexible delegation between agents
AG-UI provides human oversight and transparency
But as agents gain more autonomy, new challenges emerge. How do agents conduct secure transactions? How should APIs be designed for agent consumers? What error handling patterns prevent catastrophic failures?
Part 2 explores these extensions, emerging protocols, and practical implementation patterns.
The Commerce Challenge: When Agents Need to Spend Money
The MCP-A2A-AG-UI stack handles internal agent coordination, tool access, delegation, and oversight. As agents gain autonomy, a new challenge emerges: conducting secure transactions on behalf of users.
Why Commerce Requires New Protocols
Agents that can research, analyze, and recommend also need to execute; purchasing services, subscribing to tools, booking resources. But commerce requires capabilities beyond the core protocols:
Secure payment processing → Cryptographic verification, fraud prevention
Verified user authorization → Proof that the user approved this transaction
Spending governance → Limits, categories, approval workflows
Transaction accountability → Audit trails for what was purchased and why
MCP doesn’t handle this, it’s for tool access, not financial transactions. A2A doesn’t address it, it’s for agent coordination, not payment authorization. AG-UI provides oversight, but doesn’t solve the authorization and payment flow.
This is where agentic commerce protocols come in.
Agentic Commerce Protocol (ACP): Standardizing Agent Transactions
ACP standardizes how agents initiate purchases with merchants. It provides a programmatic checkout flow designed for agent consumers, not human shoppers.
Key Features
Programmatic Discovery → Agents can discover commerce-enabled services through standardized metadata. Similar to how MCP enables tool discovery, ACP enables product/service discovery.
Standardized Checkout → A common interface for initiating purchases, regardless of merchant platform. Whether the merchant uses Shopify, Stripe, Square, or a custom system, the ACP interface is consistent.
Transaction Context → Agents provide structured context about why they’re making a purchase, what user goal it serves, and how it fits into a larger workflow.
Receipt and Access Management → Standardized responses that include transaction receipts and access credentials for purchased services.
How ACP Works
Step 1: Agent identifies a needed resource (API access, data subscription, compute credits).
Step 2: Agent queries ACP-enabled merchant endpoints to discover available products and pricing.
Step 3: Agent initiates a transaction via the ACP interface, providing structured purchase context.
Step 4: Merchant requests authorization proof (this is where AP2 comes in).
Step 5: Upon authorization verification, merchant processes payment and provides access.
Step 6: Agent receives structured receipt and service credentials, continues its task.
What ACP Solves
Standardized Commerce Interface: Agents don’t need custom code for each merchant’s checkout flow. One ACP client works across all ACP-enabled merchants.
Structured Purchase Context: Merchants understand why the agent is making a purchase, not just what it’s buying. This helps with fraud detection and compliance.
Automated Service Provisioning: When an agent purchases API access, it automatically receives credentials and integration details in a machine-readable format.
What ACP Doesn’t Solve
Authorization Verification: ACP defines the transaction flow, but doesn’t provide cryptographic proof of user authorization. That’s AP2’s role.
Spending Governance: ACP doesn’t enforce spending limits or approval workflows. These must be implemented separately.
Fraud Prevention: While ACP provides structured context, merchants still need fraud detection systems adapted for agent behavior patterns.
Agent Payments Protocol (AP2): Cryptographic Authorization
AP2 provides cryptographic proof that a user has authorized an agent to make a specific purchase. It’s the security and governance layer for agentic commerce.
Key Features
Pre-Authorization Framework → Users define spending categories, limits, and approval requirements before agents can transact.
Cryptographic Tokens → Each transaction includes a verifiable token proving it falls within user-authorized boundaries.
Delegated Authority → Users can grant agents spending authority without sharing payment credentials or giving unlimited access.
Revocability → Users can revoke agent spending authority instantly, preventing future transactions.
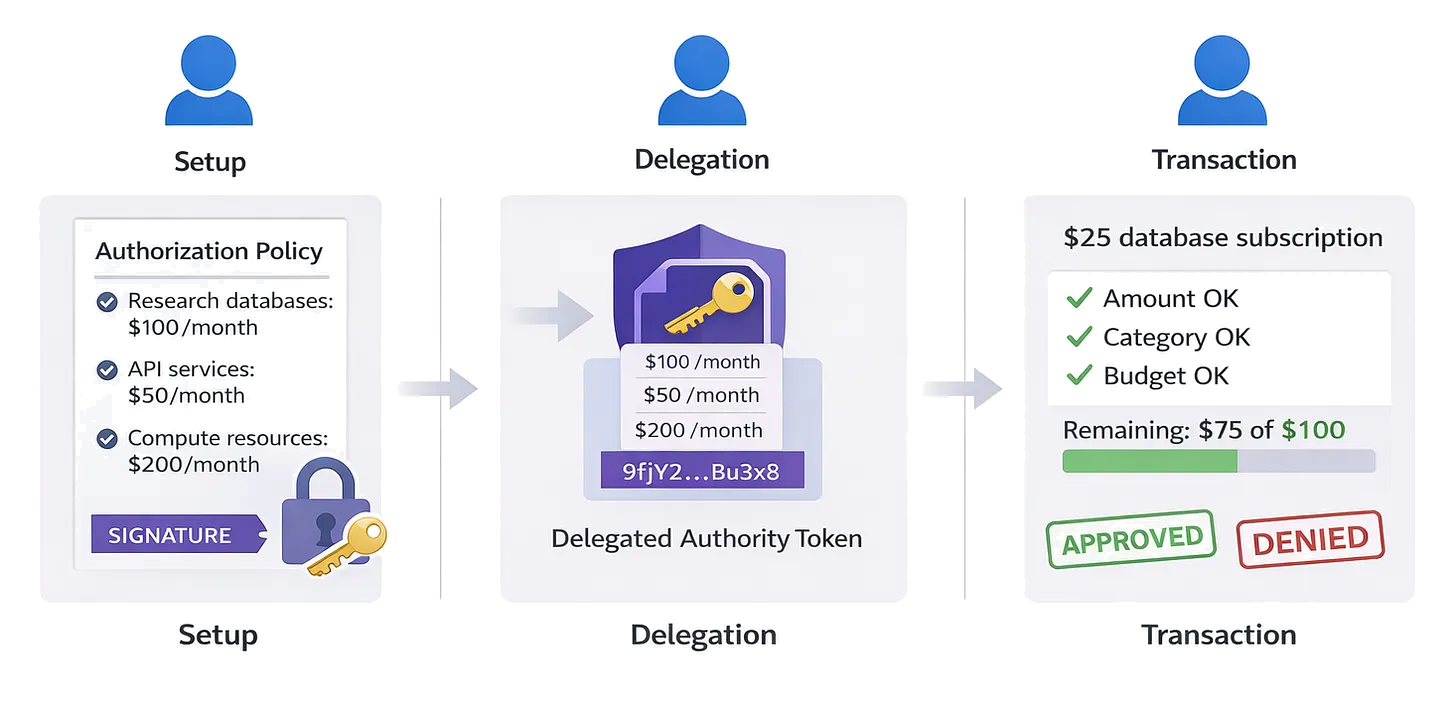
How AP2 Works
Setup Phase:
User defines authorization policies: “Agent can spend up to $100/month on research databases”
User cryptographically signs these policies
Agent receives delegated authority token
Transaction Phase:
Agent attempts purchase via ACP
Merchant requests AP2 authorization proof
Agent provides cryptographic token proving this transaction is within authorized limits
Merchant verifies token against user’s signed policies
If verified, merchant proceeds with transaction
Transaction is logged against spending limits
Audit Phase:
User reviews all agent-initiated transactions
Audit trail shows: what was purchased, when, which agent, under which authorization
User can dispute unauthorized transactions
What AP2 Solves
Trust Without Credentials: Agents can make purchases without accessing user payment credentials directly. The cryptographic token proves authorization.
Granular Control: Users specify exact boundaries—spending limits, allowed categories, approval requirements—rather than all-or-nothing agent access.
Accountability: Every transaction includes proof of which authorization policy it invoked, creating clear audit trails.
Fraud Prevention: Merchants verify cryptographic tokens, making it difficult for malicious agents to exceed authorized boundaries.
What AP2 Doesn’t Solve
Merchant Adoption: AP2 requires merchant integration. Currently, adoption is limited to early partners (Stripe, PayPal, select platforms).
Complex Approval Workflows: AP2 handles pre-authorization, but doesn’t define sophisticated workflows like “purchases over $50 require human approval.”
Cross-Agent Coordination: If multiple agents share a spending budget, AP2 doesn’t prevent them from simultaneously exceeding the limit (requires additional coordination layer).
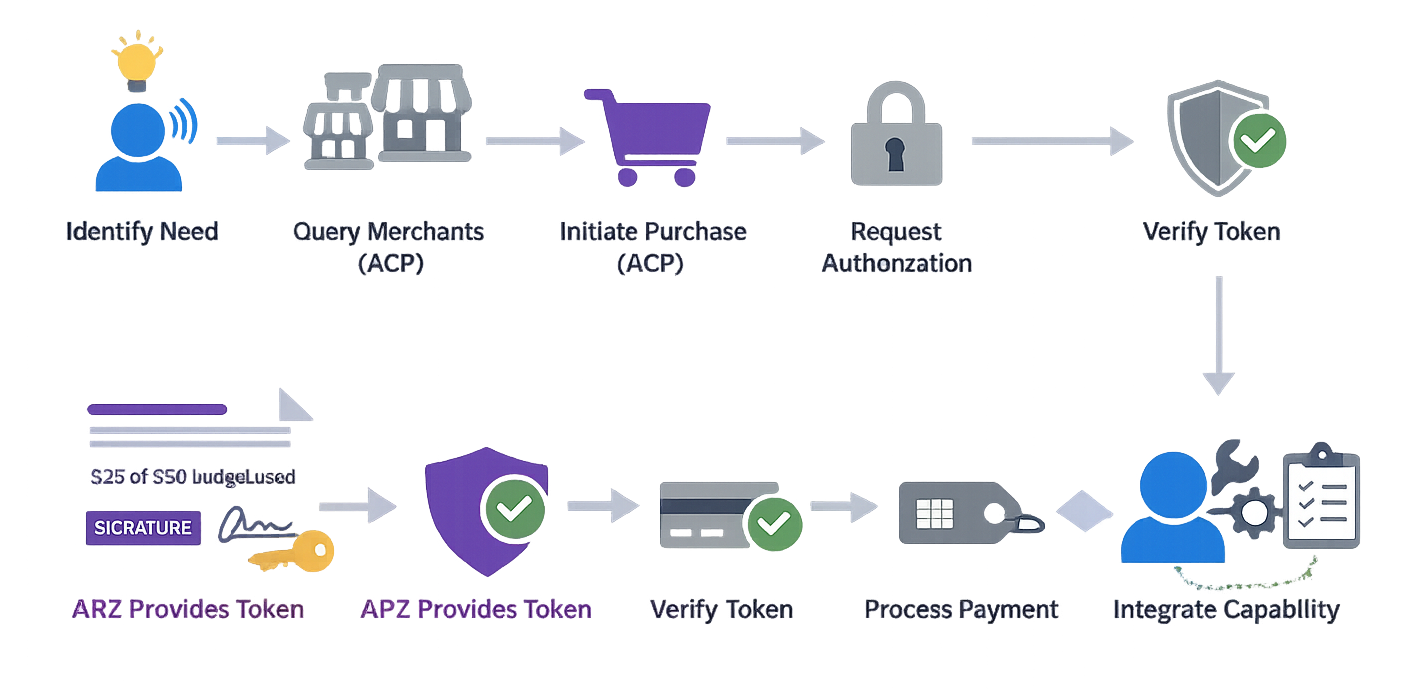
ACP and AP2 Integration Example
Let’s see how these protocols work together in a realistic scenario.
Scenario: Research Agent Purchasing Database Access
Setup:
User authorizes agent to spend up to $50/month on research databases
User signs authorization policy with AP2
Agent receives delegated authority token
Workflow:
Step 1 - Need Identified: Agent determines it needs access to a financial data API to complete a research task.
Step 2 - Service Discovery (ACP): Agent queries ACP-enabled database providers, discovers relevant service priced at $25/month.
Step 3 - Purchase Initiation (ACP): Agent initiates purchase via ACP interface, providing context: “Financial data needed for Q4 renewable energy market analysis.”
Step 4 - Authorization Request: Merchant requests AP2 authorization proof.
Step 5 - Token Verification (AP2): Agent provides cryptographic token. Merchant verifies:
Purchase amount ($25) is within limit ($50/month)
Category (research database) is authorized
Token is cryptographically valid and not revoked
Monthly budget has $50 remaining
Step 6 - Transaction Processing: Merchant processes payment, provides API credentials in structured format.
Step 7 - Service Integration: Agent receives credentials, creates MCP server wrapper for the new database, continues research task.
Step 8 - Audit Trail: User sees transaction log: “Research Agent purchased FinancialData API ($25) for renewable energy analysis task. Authorization: research_db_policy. Remaining monthly budget: $25.”
Why This Integration Matters
The agent completed a complex workflow autonomously:
Identified a need
Discovered a solution
Verified it was within budget
Made the purchase
Integrated the new capability
Continued its task
All while maintaining:
User control (pre-authorized spending limits)
Security (cryptographic verification)
Transparency (audit trail)
Accountability (clear authorization policy)
Current State and Limitations
Adoption Status
ACP: Early adoption by major platforms (Stripe, Shopify integration in development). Limited merchant support. Standards still evolving.
AP2: Backed by payment providers (PayPal, Mastercard) and AI companies (Google, OpenAI). Pilot programs running. Not yet widely deployed.
Reality Check: You can’t yet send agents to autonomously purchase from most online merchants. The infrastructure is being built, but widespread adoption is 6-12 months away.
Technical Challenges
Identity Verification: How do merchants verify an agent truly represents a user? Current solutions rely on cryptographic tokens, but this requires significant merchant infrastructure changes.
Fraud Detection: Existing fraud systems flag bot-like behavior. Agent transactions look like bots. Merchants need new fraud models that distinguish legitimate agents from malicious automation.
Session Management: Most e-commerce platforms assume human users with browsers, cookies, and sessions. Headless agent flows break these assumptions.
Dispute Resolution: When an agent makes an inappropriate purchase, who’s responsible? The user who authorized it? The agent developer? The platform provider? Legal frameworks are still developing.
When to Consider Agentic Commerce
Consider ACP/AP2 when:
Your agents need to autonomously purchase services or access
You have clear spending policies and defined authorization boundaries
You’re building on platforms with early ACP/AP2 support (Stripe ecosystem)
You’re willing to adopt emerging standards with limited merchant coverage
Wait on ACP/AP2 when:
You need broad merchant support (most platforms aren’t ready)
Your use cases involve complex approval workflows
Legal/compliance requirements aren’t clear yet
Alternative approaches (human-triggered, agent-assisted) work well enough
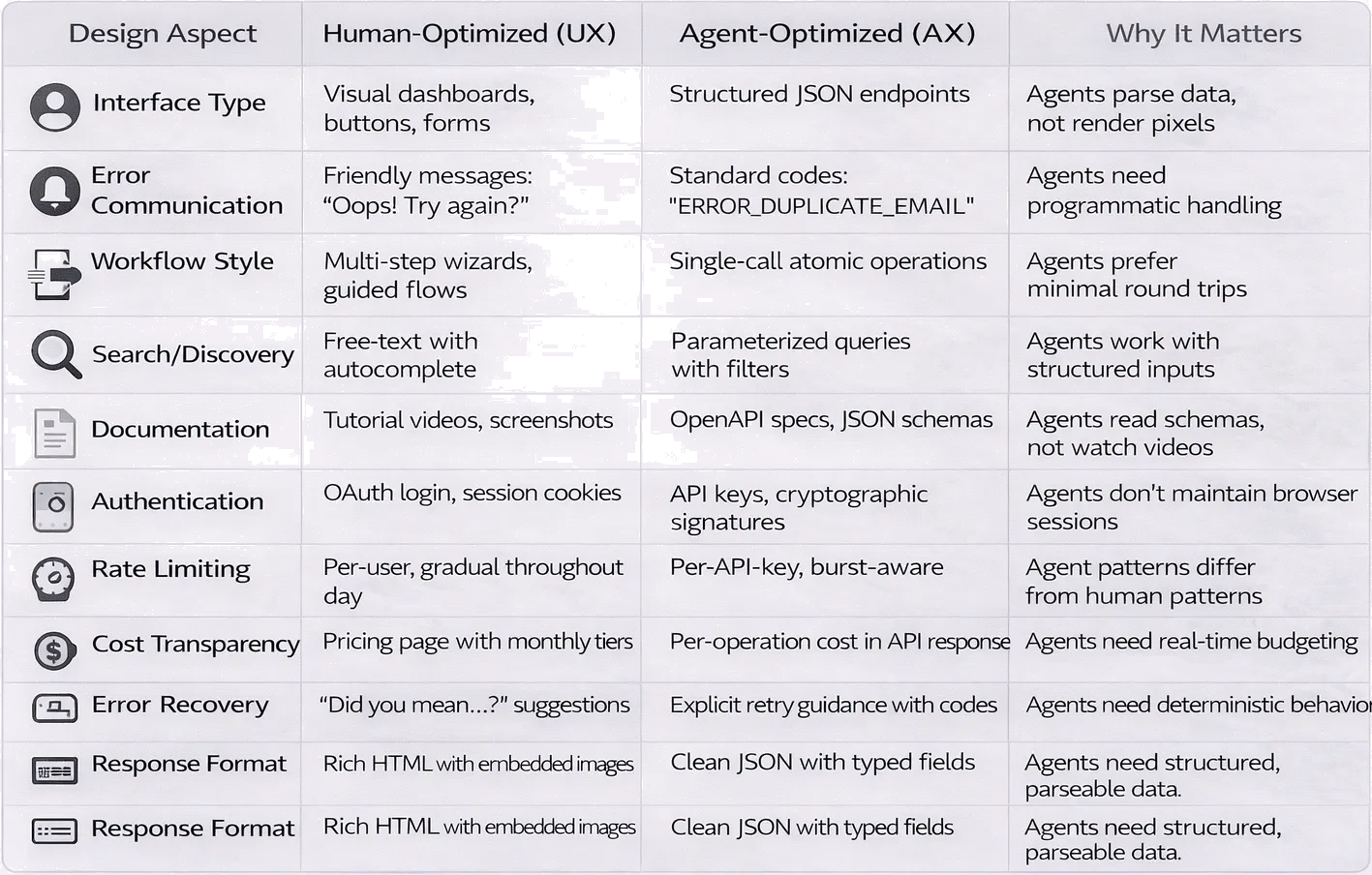
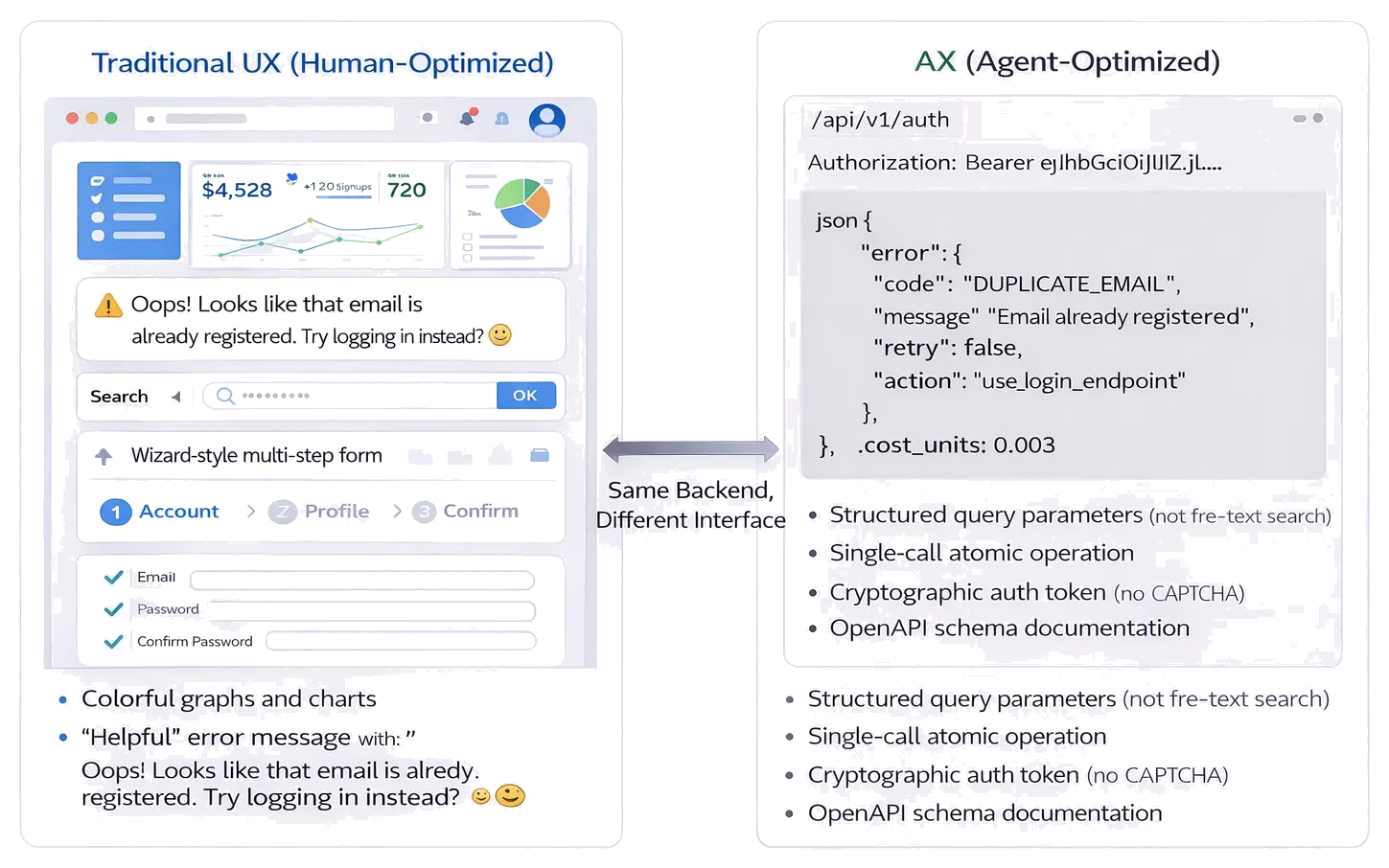
Agent Experience (AX) vs User Experience (UX)
As agents become primary consumers of services not just intermediaries for humans, API design itself must evolve.
The Fundamental Shift
Traditional UX → Design for humans using visual interfaces, manual workflows, helpful error messages, guided experiences.
Agent Experience (AX) → Design for agents consuming services programmatically, valuing clarity over aesthetics, structured data over prose, predictable behavior over flexibility.
What Agent Experience Means
1. Discoverable Capabilities
Agents need to find and understand services programmatically:
For Humans: Marketing website, tutorial videos, documentation with screenshots
For Agents:
OpenAPI specifications with complete endpoint definitions
JSON Schema for all data structures
Semantic tags describing capabilities
Embeddings-friendly descriptions for semantic search
Example API calls with expected responses
2. Predictable Behavior
Agents need consistency and reliability:
For Humans: Flexible interfaces, “smart” suggestions, adaptive UX
For Agents:
Deterministic outputs for identical inputs
Standardized error codes (not prose error messages)
Explicit rate limits and costs
Clear state management (stateless preferred)
Idempotency guarantees for safe retries
3. Structured Responses
Agents prefer machine-readable formats:
For Humans: Rich HTML, visual formatting, contextual help text
For Agents:
Clean JSON responses
Typed fields (not free text when structure exists)
Enumerated options (not open-ended strings)
Embedded context (avoid requiring additional lookups)
Consistent field naming across endpoints
4. Machine-Readable Documentation
Documentation must be parseable by agents:
For Humans: Blog posts, video tutorials, getting started guides
For Agents:
Complete OpenAPI specs
JSON Schema definitions
Example requests/responses in machine-readable format
Explicit cost-per-operation data
Error code documentation with retry guidance
Dual Interface Strategy
The best approach: provide both human and agent interfaces.
Example: Search API
Human Interface (UX):
Web UI with autocomplete
Visual result cards with thumbnets
“Related searches” suggestions
Pagination with visual navigation
Agent Interface (AX):
Clean JSON endpoint
Structured results with confidence scores
Parameterized filtering (no “smart” interpretation)
Cursor-based pagination
Semantic tags on results
Shared Backend: Both interfaces access the same search logic, just presenting it differently.
The Business Case for AX
Today: Your API has 1,000 human users making 10 calls/day = 10,000 daily calls
Tomorrow: 100 agents discover your API, each making 100 calls/day = 10,000 additional daily calls
Question: Is your infrastructure ready for agent-scale consumption?
Rate limits designed for human patterns (requests spread throughout the day) break when agents parallelize
Authentication flows assuming manual login don’t work for headless agents
Error messages written for human debugging aren’t parseable by agent retry logic
Pricing models based on “users” don’t make sense when one user has 10 agents
Designing for Agent Consumers
Rate Limiting
Human Pattern: Gradual requests throughout the day
Agent Pattern: Burst parallelization, then idle
AX Solution:
Time-window based limits (1000 requests/hour) instead of per-minute
Explicit queuing with wait-time estimates
Batch endpoints for common multi-call patterns
Authentication
Human Pattern: OAuth login, session cookies, periodic re-auth
Agent Pattern: Long-lived API keys, no sessions, frequent automated calls
AX Solution:
API key authentication with clear rotation policies
Cryptographic signatures (no session state)
Scope-limited tokens (read-only vs write access)
Error Handling
Human Pattern: Descriptive messages like “Looks like that email is already registered! Try logging in instead?”
Agent Pattern: Need error codes for programmatic handling
AX Solution:
json
{
"error": {
"code": "DUPLICATE_EMAIL",
"message": "Email already registered",
"retry": false,
"action": "use_login_endpoint",
"details": {
"field": "email",
"provided_value": "user@example.com"
}
}
}Cost Transparency
Human Pattern: Pricing page with feature tiers
Agent Pattern: Need per-operation costs for budgeting
AX Solution:
Include cost in API responses:
"cost_units": 0.003Provide cost estimation endpoints: “How much would analyzing this dataset cost?”
Rate limit headers include cost spent:
X-Cost-Remaining: 97.5
Real-World Example: Database API
Human Version (Traditional UX):
Web UI for running queries
Visual table browser
Export button for CSV downloads
Helpful query suggestions
Agent Version (AX):
Structured query endpoint accepting JSON
Result streaming for large datasets
Metadata including row counts, query costs
Query validation endpoint (before execution)
What Changed:
Same database backend
Agent version prioritizes: structure, cost visibility, programmatic validation
Human version prioritizes: visual exploration, guided workflow, export convenience
Error Handling and Resilience Patterns
Multi-agent systems with protocol integration face unique error handling challenges. Here are essential patterns.
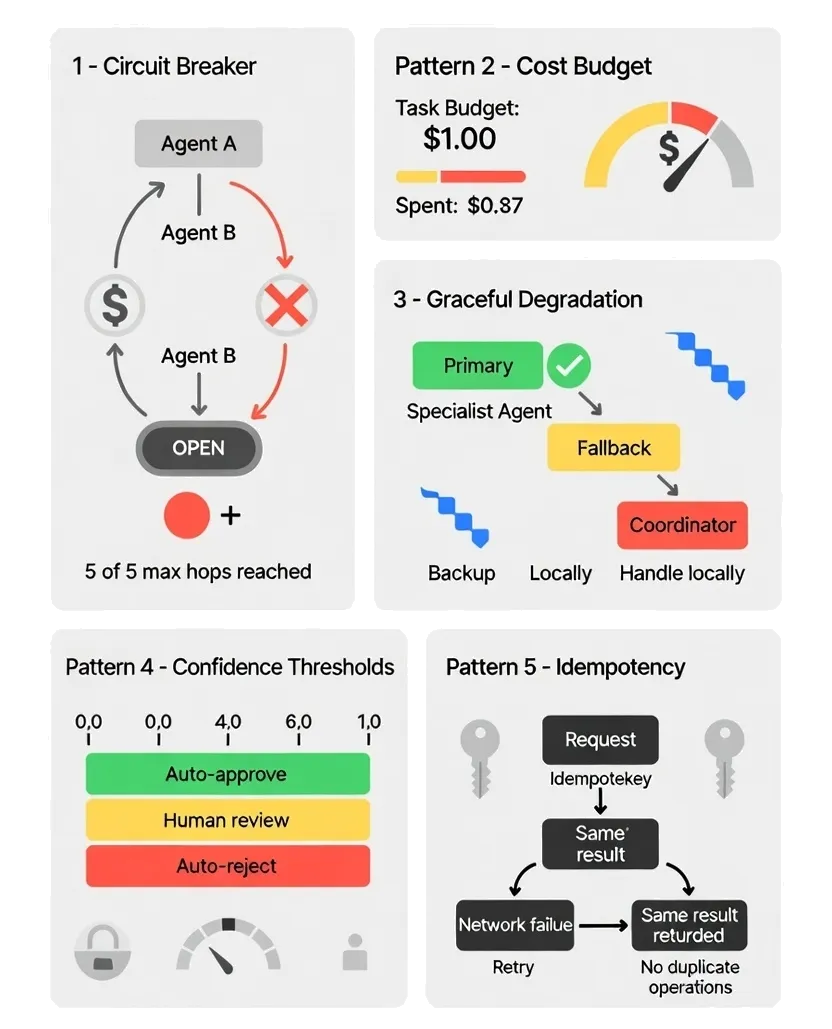
Pattern 1: Circuit Breakers for Delegation Loops
Problem: Agent A delegates to Agent B, which delegates back to Agent A, creating infinite loops.
Solution: Track delegation chains, implement hop limits.
class DelegationCircuitBreaker:
def __init__(self, max_hops=5):
self.max_hops = max_hops
self.delegation_chain = []
def delegate(self, from_agent, to_agent, task):
# Check for loops
if to_agent in self.delegation_chain:
raise DelegationLoopError(f"Loop detected: {self.delegation_chain}")
# Check hop limit
if len(self.delegation_chain) >= self.max_hops:
raise MaxHopsExceeded(f"Exceeded {self.max_hops} delegation hops")
self.delegation_chain.append(to_agent)
# Proceed with delegation via A2APattern 2: Cost Budgets per Agent
Problem: Recursive A2A delegation causes cost overruns.
Solution: Assign cost budgets, track spending across delegation chains.
class CostGovernor:
def __init__(self, budget_per_task=1.00):
self.budget = budget_per_task
self.spent = 0.0
def check_budget(self, estimated_cost):
if self.spent + estimated_cost > self.budget:
raise BudgetExceededError(
f"Task budget ${self.budget}, spent ${self.spent}, "
f"operation would cost ${estimated_cost}"
)
def record_cost(self, actual_cost):
self.spent += actual_cost
remaining = self.budget - self.spent
if remaining < 0.10: # Warning threshold
emit_warning(f"Only ${remaining} remaining in budget")Pattern 3: Graceful Degradation
Problem: When a specialist agent fails, the entire workflow stops.
Solution: Define fallback strategies for each delegation.
class ResilientCoordinator:
def delegate_with_fallback(self, task, preferred_agent, fallback_agent=None):
try:
return self.a2a_delegate(task, preferred_agent)
except AgentUnavailableError:
if fallback_agent:
return self.a2a_delegate(task, fallback_agent)
else:
# Last resort: coordinator handles it directly
return self.handle_locally(task)Pattern 4: Confidence Thresholds for Human Escalation
Problem: Knowing when AG-UI intervention is needed.
Solution: Define confidence thresholds, automatically escalate low-confidence decisions.
class ConfidenceBasedOversight:
def __init__(self, auto_approve_threshold=0.85):
self.threshold = auto_approve_threshold
def make_decision(self, decision, confidence):
if confidence >= self.threshold:
# High confidence: proceed automatically
return self.execute(decision)
else:
# Low confidence: request human review
return self.request_human_approval(decision, confidence)Pattern 5: Idempotency for Retry Safety
Problem: Network failures cause agents to retry operations, potentially duplicating actions (sending emails twice, charging cards twice).
Solution: Implement idempotency keys in MCP tool calls.
class IdempotentToolCall:
def __init__(self, mcp_client):
self.client = mcp_client
self.completed_operations = {}
def call_tool(self, tool_name, params, idempotency_key):
# Check if already completed
if idempotency_key in self.completed_operations:
return self.completed_operations[idempotency_key]
# Execute operation
result = self.client.call(tool_name, params)
# Cache result
self.completed_operations[idempotency_key] = result
return result⚡ From Patterns to Production If these error handling patterns are useful, you'll want the implementation deep-dives coming next: → Building observability for multi-agent systems → Testing strategies for non-deterministic agents → Deployment patterns for agent orchestration → Performance optimization across protocols
Get practical implementation guides in your inbox Subscribe here Real code. Real trade-offs. Real production experience it’s free, and I’ll never sell you anything
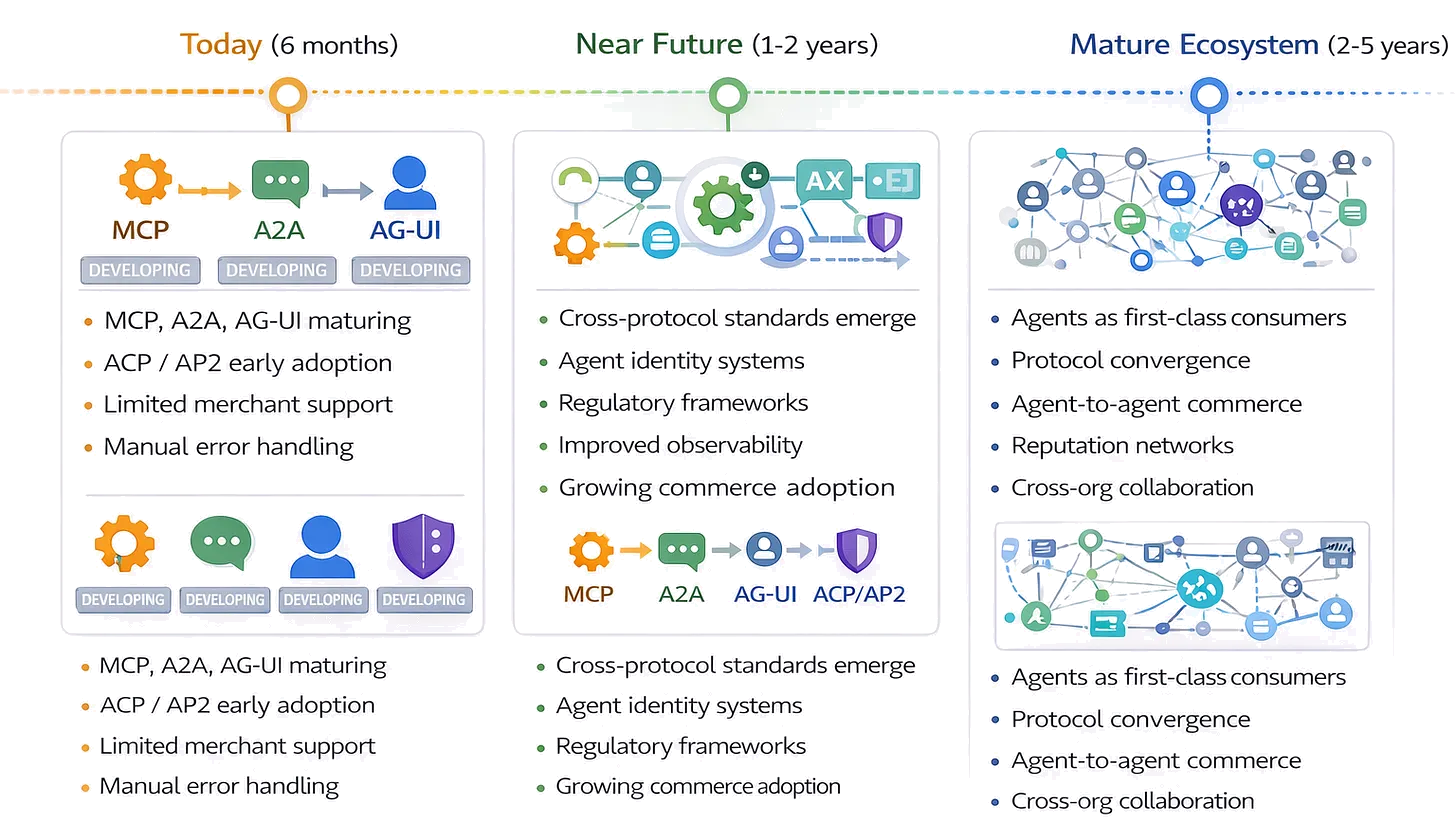
What’s Next: The Future of Agent Protocols
Short-Term Evolution (6-12 months)
Protocol Maturation:
MCP server ecosystem grows (more integrations, better tooling)
A2A capability discovery becomes more sophisticated (semantic matching)
AG-UI standards consolidate (event types, intervention patterns)
Commerce Adoption:
Major e-commerce platforms add ACP support
AP2 authorization frameworks mature
First wave of agent-autonomous purchases in production
Tooling Improvements:
Better observability for multi-protocol workflows
Cost attribution across delegation chains
Testing frameworks for protocol integration
Medium-Term Trends (1-2 years)
Cross-Protocol Standards:
Error handling conventions across MCP, A2A, AG-UI
Cost reporting standards (unified across all protocols)
Observability integration (distributed tracing for agent workflows)
Agent Identity:
Persistent agent identities across protocols
Reputation systems (which agents are reliable?)
Cross-platform agent portability
Regulatory Frameworks:
Compliance standards for agent transactions
Liability models for agent actions
Privacy requirements for agent data access
Long-Term Vision (2-5 years)
Agent Ecosystem Maturity:
Agents as first-class API consumers (equal to humans)
Agent-optimized services outperform human-optimized for automation use cases
Economic incentives for building agent-friendly infrastructure
Protocol Convergence:
Industry consolidation around winning standards
Cross-platform interoperability becomes seamless
Agent development frameworks abstract protocol complexity
New Challenges:
Agent-to-agent commerce (agents paying each other)
Cross organizational agent collaboration
Agent reputation and trust networks
Key Takeaways
Agentic Commerce
ACP standardizes how agents initiate purchases. AP2 provides cryptographic proof of authorization. Together, they enable secure agent-driven transactions within user-defined boundaries.
Reality Check: Emerging standards, limited adoption, 6-12 months from mainstream use.
Agent Experience Design
APIs must serve both human and agent consumers. Agent-optimized design prioritizes:
Structured data over visual interfaces
Predictable behavior over flexibility
Machine-readable documentation over tutorials
Cost transparency over pricing pages
Error Handling Patterns
Multi-agent systems need:
Circuit breakers for delegation loops
Cost budgets per task
Graceful degradation with fallbacks
Confidence thresholds for human escalation
Idempotency for retry safety
The Future
Protocol ecosystems will mature, commerce adoption will grow, and agent-optimized infrastructure will become standard. The teams building with these protocols today are establishing competitive advantages for tomorrow.
Final Thoughts: From Protocols to Production
Understanding MCP, A2A, AG-UI, ACP, and AP2 is foundational knowledge. But production multi-agent systems require more than protocol adoption:
You need:
Error handling that prevents catastrophic failures
Cost controls that prevent budget overruns
Observability that shows what agents are actually doing
Fallback strategies when specialists fail
Clear boundaries for when humans must intervene
The protocols give you:
Standardized tool access (MCP)
Flexible agent coordination (A2A)
Transparent oversight (AG-UI)
Secure transactions (ACP/AP2)
You still build:
Circuit breakers and hop limits
Confidence scoring and escalation logic
Idempotency and retry strategies
Cost attribution and budgeting
Audit trails and compliance frameworks
The protocols are infrastructure. The architecture is yours to design.
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 🎯 QUICK ASSESSMENT
Does your use case need agentic commerce NOW or should you wait? Score yourself: □ We need agents to purchase services autonomously (+2) □ We're on Stripe/Shopify ecosystem (+2) □ We have clear spending policies defined (+1) □ We can wait 6-12 months for broader adoption (-1) □ We need integration with random merchants (-2) □ Legal/compliance frameworks are unclear (-1) Your Score: 4+: Start piloting ACP/AP2 now 1-3: Design authorization models, wait for stability 0 or less: Use human-triggered, agent-assisted flows 💬 Reply with your score and use case
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━
What Topics Should I Cover Next?
I want to hear from you. What multi-agent challenge are you facing?
Implementing error recovery in production?
Choosing between MCP and A2A for specific use cases?
Adding human oversight without killing automation benefits?
Preparing for agentic commerce?
Designing agent-friendly APIs?
Something else?
Drop a comment with your biggest question. I’ll address the most common patterns in the next deep-dive.
Subscribe to The Neural Blueprint
By Vijendra
Deconstructing the architecture of modern AI systems